Do you know what’s getting through?
Many threats now bypass Microsoft 365 and legacy Secure Email Gateways. From business email compromise to vendor impersonation, we help you uncover what you’re missing, and take the next step toward better protection.
Legacy SEGs aren’t built for today’s threats.
SEGs were designed to stop traditional spam and malware, not today’s behavioural attacks. Targeted phishing, social engineering, and impersonation threats are now crafted to bypass these defences entirely.
Request a Free Risk Assessment- Invoices from spoofed vendors
- Emails from real accounts that were compromised
- Zero-link phishing messages that look legitimate
- Sensitive data sent or shared without detection
If you’re relying solely on Microsoft or a legacy SEG, you’re likely exposed.
See the gaps. Act before they’re exploited.
Our guided assessment highlights email-based threats your current tools don’t catch—no platform changes, no new software to install.
Get my risk snapshotFor security and IT leaders ready to get ahead of the curve.
Whether you’re managing compliance risk, IT security, or incident response, this assessment gives you the clarity you need—without complexity.
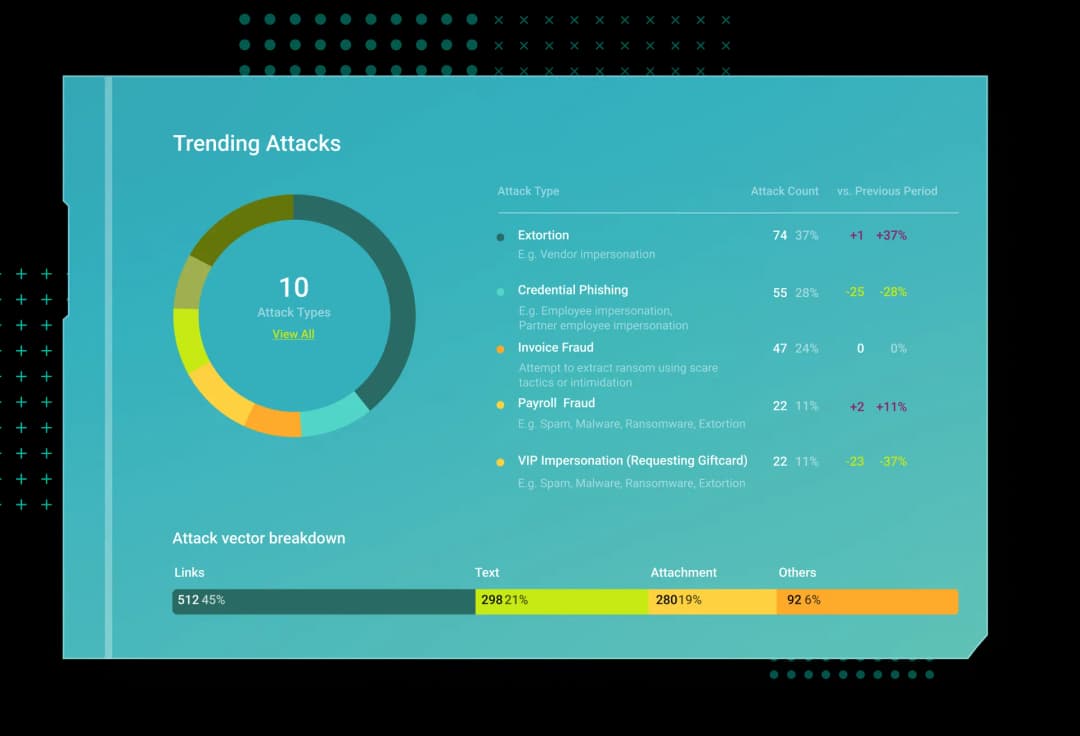
Behavioural intelligence, not signature-matching.
Modern attacks don’t look suspicious on paper. They pass authentication, they come from real-looking accounts, and they target the right person at the right moment. Stopping them takes more than rules and reputation lists.
Behavioural AI maps every employee’s normal patterns—the people they talk to, the times they log in, the locations they work from, the systems they use. When something deviates from that pattern, even subtly, it gets flagged. Before it reaches the inbox.
See how training adapts to real threats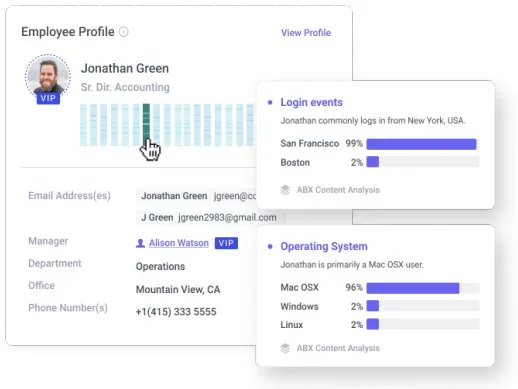
Not a sales call. Not a demo. Just the truth.
No installs. No platform changes. Just a confidential, insight-driven review of what threats are reaching your organisation, and what to do next. Powered by best-in-class behavioural AI, delivered by trusted local experts.
Used by teams who’ve outgrown legacy defences.
We had Microsoft and a SEG, but real threats were still hitting inboxes. This gave us the clarity and the next steps we were missing.
Your email tools weren’t built for this.
Modern threats are subtle. The risk is real. We’ll help you understand your exposure and plan your next step—clearly, calmly, and with zero disruption.